Virus Prevention
This text was first published in the free What-Computer magazine. I found it so good that I wanted to translate it in french. This page is here only for those that prefer the original version. You can have a look on the doc file (best presentation).
Virus
‘Love Bug’ leaves a trail of broken hearts
You never know when they might strike, and what damage they might do if they do hit. The computer virus is a nasty little beast but what can do to limit its impact ? Billy Williams of Norman Data Defence, the anti-virus specialists, looks at what has happened and gives a crucial insight into beating the bugs.
You only have to look at the media coverage on the Love You’ bug to see how much damage a single virus can cause. This, however; is nothing new: Melissa brought thousands of email servers to their knees in March 1999 and ever since, home users and corporate businesses alike have waited for the next ‘strike’.
But who is to blame? Well, we could start at Microsoft’s door but this would not be totally fair. Microsoft has written many features into its newer operating systems that give PC users functionality that they could have only dreamed about two years ago. To suddenly remove these features and apply security instead would leave users feeling they were running a Model T Ford version of their once proud VS turbo-charged sports car. This is the old argument; PC functionality versus PC security.
The operating system ‘interfaces’ now available on most PCs are there for software to take advantage of, allowing seamless interaction between different applications. For the majority of packages this is excellent news, however; our concerns lie with the small minority of mindless virus writers out there.
So, where is this threat coming from? Simply, anyone who knows how to write a VBS script can cause mayhem on the Internet, because the code written can interface directly with the operating system on your machine. So far; the damage has been minimal in that the attacks have been blatant and discovered almost immediately. The ‘Love Bug’ is a good example of how easy it is to cause problems. This code was written by a student in Malaysia who sent it to several contacts; within minutes the virus was replicating on networks around the world.
What is so frightening is that the VBS author could quite easily ‘time-bomb’ many of the effects of the virus, making the damage only apparent after many days or weeks, by which time the virus could very easily have infected most machines connected to the Internet. Furthermore, it is known that there are loopholes in the settings on applications, such as Outlook Express, which if hit by a virus allow it to add itself invisibly to the PC.
The ‘Love Bug’ virus was not that dangerous. Some of the subsequent mutations, however, were altered to delete files from your hard drive if the script was run. By this time, most people were very much aware of the threat and would have been very wary of the unexpected email.
Users should be wary of emails that arrive with attachments they are not expecting. If in doubt, contact the sender first to question the email and make sure you keep the virus detection files up-to-date. If the scanner does not know about a virus, it will be hard, if not impossible, to detect it in the first instance.
Although there are over 40,000 known viruses, only about 160 are actually registered as being ‘in the wild’. These viruses are constantly being reported as detected on the Internet, but this begs the obvious question: Why? Surely everyone is using Virus Control software?
No, not true. Most infections reported come from users, either with no virus control, or those who have out-of-date software The infection is only detected when infected attachments are sent to properly protected users. It is these users with up-to-date software who prevent the mass spread of viruses.
Think about it. The only reason the ‘Love Bug’ virus has died a death is because all the gateway servers are now actively seeking out this code and deleting it before allowing a blank email to pass.
So, from earlier discussions, everyone knows you don’t open unexpected attachments without checking first, but what if there isn’t an attachment to run? What if the email is from someone you know and has nothing attached?
Sure, you would open the email, why not? Would you phone someone who sends you a plain email, with no visible attachments, to check if it is genuine and not an infection? Now you can see the problem. KAK is just one virus which looks like that. Using a Windows command, it is actually imbedded into a signature in the email, so there is no attachment to run. However, open the email, or preview it in your Outlook client, and the next thing you know you have been infected.
Microsoft is aware of this and patches are available on its websites which cover these issues. Take a look at www.microsoft.com for further information.
But where does the virus market go from here? There are so many risks possible that it is only a matter of time before connecting to a rogue website will activate one of these interfaces, causing changes and the uploading of your files to the Internet. These are all potential threats, and ones that need watching closely.
In all of the issues raised, and these are but a few, there is a simple rule written between the lines. If you don’t keep up-to-date with the virus control software then you are simply inviting trouble somewhere along the line. And, common sense must prevail when dealing with email, as running attachments without prior reflection can only land you in hot water.
All it takes is common sense
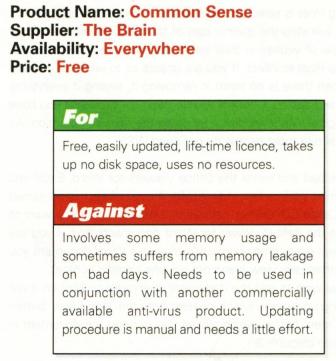
What follows is a fictional review on a non-existent anti-virus product, written by Ian Higginbotham, managing director Norman Data Defense Systems (UK). However, the message that it contains is very real. In the wake of the ‘LoveBug’, people have found it very easy to blame the anti-virus (AV) companies for the tide of woes that have beset them. In fact, users have played a huge part in the rapid propagation of these new viruses by taking no heed of warnings dished out by IT departments and the anti-virus industry. This is not the fault of the end users – the blame lies with those who have failed to get the right message across and make it stick
Introduction
This product is the most common anti-virus solution available today and yet it is the least used. This is probably due to the fact that many people think that the product is too difficult to use and understand. This review will dispel some of those fears, providing a valuable insight into using the application.
Installation and training
Installation can take as long as five minutes and the training will take as long as it takes for each individual to read this review.
How the product works
The product uses a rules-based system for identifying a virus. This system is not infallible and may sometimes fall prey to a memory leakage, needing occasional updates.
Understanding the reason for the rules
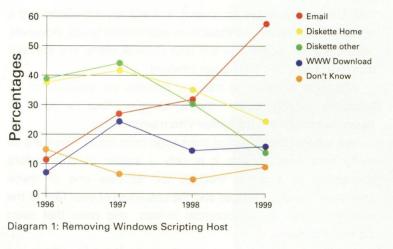
Before we explain the rules of using ‘Common Sense’, we need to understand how viruses make their way onto a computer. At the moment 60 per cent of viruses come from email (see figure 1). This is a huge increase on previous years and is largely due to email mass-mailers, such as Melissa and the ‘Love Bug’. The second largest source is still floppy diskettes, of which two-thirds are brought in from home. This is a great reason for having a double licence of Common Sense as it can be used at home as well.
The second thing to consider is that 63 per cent of viruses are macro viruses, but these are not the ones that tend to cause the most infections, as we shall see.
So, with two-thirds of infections coming from email, we need to look closely at how they infect us. Up until a couple of years ago, the adage used to be that ‘you cannot become infected if you open an email or preview it; you will only become infected if you run the attachment’. This changed when the likes of Bubbleboy appeared, which infected your machine under certain circumstances if you previewed the email, let alone opened it.
However, this was not the case with ‘Love Bug’, which came one year after the original Melissa virus and a few months after ExploreZip. Those people that were infected with Melissa were educated on how to not become infected, but immediately forgot all that they had been taught when ExploreZip went into the wild. So IT departments trained all their staff, again, and then they promptly forgot it all again when ‘Love Bug’ hit and went round getting infected and infecting others. The message is just not getting through!
Finally, we need to understand that commonly available, commercial AV software has given us all a false sense of security. We expect the software to catch the viruses for us and so we open emails with utter abandon.
Before the advent of the mass-mailers this was generally adequate as the AV companies shared information on new viruses, and so they generally had a fix available before the virus spread too far and got out of control.
Now we have the situation where if one AV company had a fix before a virus went into the wild it would not take long for people, and the press, to put two and two together to make five, and shout ‘foul!’, saying that a particular AV company was writing viruses and releasing a fix for them at the same time.
If I had a pound for every time I heard that argument then I would be the managing director of an AV Company. Hang on, I am the managing director of an AV Company. Well I told you so.
Of course, it is not true, but we all blindly trust in a product that needs some serious evolution to reach the same level of defence as we expected from these products as little as one year ago.
This is why ‘Common Sense’ works so well. It gives us another layer of defence in our fight against viruses and here is the good news – ‘Common Sense’ can co-exist on any PC with any other AV product, without any clashes or conflicts, so you do not need to change your current AV software to one that is compatible with ‘Common Sense’.
The 10 rules of Common Sense
-
Before anything else, boot the computer and go into the CMOS (the computer manual will tell you how to do this if you have not done it before) and change the boot sequence from ‘A then C’ to either ‘C then A’, or preferably to ‘C Only’. This will now stop you from becoming infected by all of the pure Boot sector infectors and all partition infectors (it will not, however, stop multi-partite viruses in their boot sector infecting stage).
If you need to boot from a floppy at any stage, it is a 30-second job to change it back to ‘A then C’, providing you remember to put it back to safe mode when you have finished using your boot floppy.
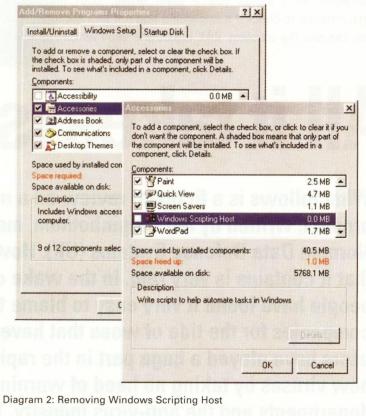
- If you do not use Windows Scripting Host (WSH) then remove it. (see diagram 2). Go into ‘Control Panel’ and then ‘Add/Remove Programmes’. Select the ‘Windows Setup’ tab, select ‘Accessories’ and then the ‘Details’ button, and if the Windows Scripting Host is selected, then deselect it and click on ‘OK’.
This will stop the greater part of the new Melissa and ‘Love Bug’ type of viruses in their tracks, as they need the Windows Scripting Host to infect. If you are unsure as to whether you use WSH then there is no harm in removing it, seeing if everything works, and adding it back if you do need it – providing you have your original Windows disk – by doing the reverse operation. As a general rule most people do not need WSH. - Download and install the Office Viewers for Word, Excel and PowerPoint (all free from Microsoft). A copy of each is contained on the Office CD. During installation it will ask you if you want to use it as the default viewer for Word documents and, if you say ‘Yes’, then every time you double click on a Word document you will automatically view it and not run any harmful content.
If you wish to edit the document, then right-clicking on it will now bring up a menu which includes both the ‘WordView’ button and a ‘Open’ button which allows you to open the document in Word (see diagram 3).

- Change how you save documents to Rich Text Format (RTF) if you are not a big user of macros, or if the document contains no macros. RTF cannot support macros and therefore harmful macro content cannot be passed from document to document. You will not send a macro virus to someone if you send out the document like this.
- Make sure that Explorer shows all extensions by selecting ‘View’ and ‘Folder Options’ and then deselecting ‘Hide file extensions for known file types’. If someone has added an extension to a file that is an ‘exe’ at the end of another extension, you will automatically be able to see the correct extension and have a warning that all is not as it seems.
- Disable ‘Options’ in Browser software that you do not use often, such as Java Script and ActiveX, or at least set the software to prompt you each time it detects it on a web page. At least you then have a choice of whether you run it or not according to the level of trust you place on an individual website, and whether you consider the risk of running something that may be harmful is worth it.
At the same time disable HTML support within your email software so that harmful code is just not run. And, while you are at it, do the same with your NewsReader software as well. - When you get an email with an attachment, think about it before you open it. Is it an email with a strange title? Does the attachment have an odd name? Is it something I was expecting from this person? Is it a person I converse with by email often? (I got sent copies of ‘Love Bug’ by people and I have no idea how I got onto their address list!) Does the attachment have a strange extension? If you are happy then open the email, but do not blithely then run the attachment. First of all detach it and place it in a quarantine directory (mine is just called ‘Downloaded’ and is in ‘My Documents’). Once you have detached it, scan the directory to make sure it is not a virus that the AV software already knows about.
Many people will now say: ‘But saving it to disk would have meant the AV software real-time scanner has already scanned the file, so why scan it again?’ This may be so, but what if the real-time scanner is not running or has been disabled somehow? I would rather be safe than infected. I’m sure you would too.
Now make sure that the extension of the saved file is the same as the extension of the attachment to the email. Remember, if you are in any doubt at all about an email or an attachment, then delete it and/or ring the person who sent it to you and ask them if they meant to send it and what it is. If they say they never sent you anything then tell them they may be infected and send them a copy of ‘Common Sense’. - Stop sending out so many attachments yourself and discourage people who do it to you as well. I am constantly bombarded with attachments that could just have easily been a URL. The problem is that as my mailbox gets bigger, I tend to delete emails with attachments first, and so stand the chance of losing a good piece of information, whereas if it was a URL, the email is of no size at all and I can refer to the piece of information whenever I need it -providing the URL stays the same of course!
- Back up your data regularly to a different location so that if you do inadvertently become infected, and your files become corrupted, then at least you have a copy of most of them stored somewhere else.
- Learn about hoaxes: What they are and how to spot them. A good place to start is www.kumite.com/myths. You see, you are using ‘Common Sense’ already!
None of these rules are any more important than the others so you need to use them all for ‘Common Sense’ to work correctly and remember, you must also use a piece of AV software that is both current and applicable.
By that I mean that it is as up-to-date as you can get it, (I would consider ‘within the last week’ as current) and it is capable of doing the job it says it can. Again, have a look at somewhere like www.virusbtn.com which tests AV software on a regular basis and tells you what it considers to be software capable of detecting the current crop of viruses that are in the wild.
Conclusion
I rate ‘Common Sense’ very highly and would recommend it to everyone without hesitation. As to the ruggedness of the software, there are a few question marks as to whether it is as efficient on a Monday morning or a Friday afternoon as it is during the rest of the week. All it takes is a little bit of thought to give you an enhanced level of protection over that which you already should have. Having said that though, for a freebie, it does an excellent job – especially if allied to another piece of AV software.